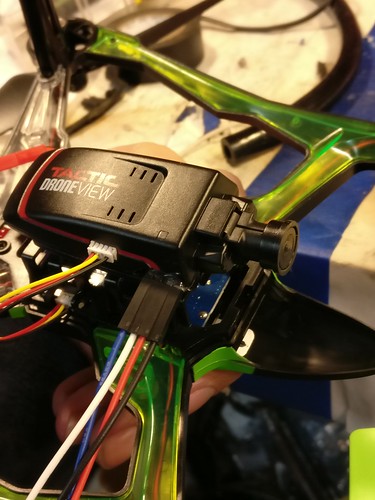
DroneView WiFi Camera, Part 3
Written 2017-01-01
Tags:WiFi DroneView UART Serial
This one time, I just took the darned thing apart
A third pass at the previous two posts.Serial Config
Felipe says the default baudrate for HiSilicon Hi3518 IP Cams is 115200 Baud, 8N1PCB
Only connect RX, TX, and GND. Additionally, the PCB test points are not quite 0.1 inch pitch, so I had to bend some pins to get it to connect. Additionally, the 3.3V port does not seem very useful, as it appears the device will become confused if supplied directly with 3.3V without 3.7V from the lithium battery pack. I suspect the WiFi radio is powered from 3.7v. After a little solder and knifework, I have a functional serial port.
Sadly I did not photograph it before reassembly. It is simply solder and hot glue for strain relief.
Rooting the Device Locally
Stop the device very early during startup, and append init=/bin/sh to the boot arguments, then do the normal SPI boot.
Hit any key to stop autoboot: 1 ^H^H^H 0
hisilicon #
hisilicon # setenv bootargs mem=42M console=ttyAMA0,115200 root=/dev/mtdblock2 rootfstype=jffs2 mtdparts=hi_sfc:1M(boot),2944K(kernel),10112K(rootfs),1280K(config),64K(key) init=/bin/sh
hisilicon # sf probe 0;sf read 0x82000000 0x100000 0x300000;bootm 0x82000000
...system boots here...
# cat /etc/passwd
root:$1$dfU0W8J6$vKtbAXdyZmq5GbYveqnnJ.:0:0::/root:/bin/sh
Preparing a backdoor
In UNIX, a second user account may be added with the same user-ID. This is easily prepared using openssl
rsaxvc@x220:~$ openssl passwd -1
Password:
Verifying - Password:
$1$DGtWAnSP$opJzjiYrVEy82GT9btLCo/
rsaxvc@x220:~$
Adding a backdoor
Previously, we created our backdoor, now we install it using pipes. I show a demo yoursalt - 1111 hash, but you should use the result from OpenSSL.
# cat /etc/passwd
root:$1$dfU0W8J6$vKtbAXdyZmq5GbYveqnnJ.:0:0::/root:/bin/sh
# echo 'rsaxvc:$1$yoursalt$1111111111111111111111:0:0::/root:/bin/sh' >> /etc/passwd
# cat /etc/passwd
root:$1$dfU0W8J6$vKtbAXdyZmq5GbYveqnnJ.:0:0::/root:/bin/sh
rsaxvc:$1$yoursalt$1111111111111111111111:0:0::/root:/bin/sh
# mount / -o remount,ro
# sync
Cracking the network password
rsaxvc@rsaxvc:~/code/john-1.8.0/run$ nice nice ./john ~/passwd
Loaded 1 password hash (md5crypt [MD5 32/64 X2])
Will run 24 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
ev1324 (root)
1g 0:00:20:12 3/3 0.000824g/s 104157p/s 104157c/s 104157C/s ev199c..ev1r10
Use the "--show" option to display all of the cracked passwords reliably
Session completed
rsaxvc@rsaxvc:~/code/john-1.8.0/run$ telnet 192.168.234.1
Trying 192.168.234.1...
Connected to 192.168.234.1.
Escape character is '^]'.
ipc login: root
Password:
Welcome to HiLinux.
None of nfsroot found in cmdline.
#
Next Steps
- Look for command injection in the webapp.
- Look at how the Android and Windows actually work
- Request source code from the vendor